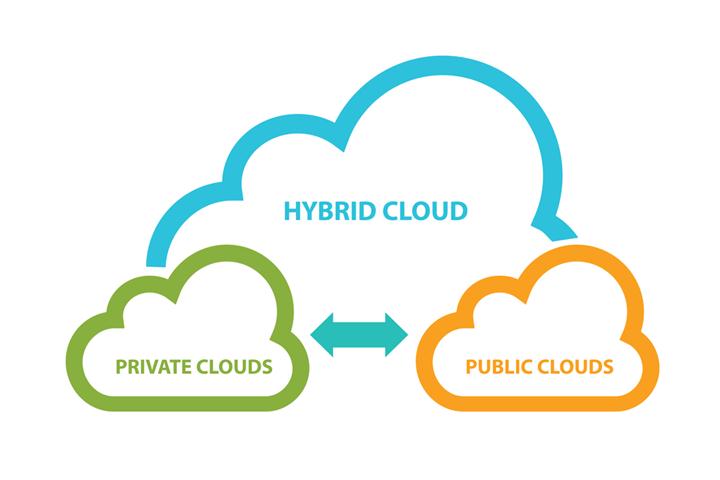
According to a 2016 report by RightScale, 71% of companies make use of hybrid cloud computing services, while only 6% use private cloud services exclusively. Managed hybrid cloud computing security solutions make use of both public and private clouds, delegating sensitive information and activities to the private cloud while ordinary data traffic gets handled by the public cloud.
Hybrid cloud services are cost-effective, allowing access to a larger scale of resources while still providing the necessary security measures to protect valuable and sensitive data. Such services can be customized to the needs of individual clients, providing functionality and value while reducing costs.
Managed Hybrid Cloud Computing Security Solutions
Integrating the public and private spheres of the broader cloud network is one of the key requirements of an effective hybrid cloud strategy. Accessing the public cloud with broader resources for non-sensitive traffic and transitioning to the private cloud when required, calls for data protection strategies, traffic visibility, and control over access privileges.
Control over user privileges is known as managed access, which ensures that only authorized user identities are able to make use of resources on both the public and private clouds while enabling swift identification and authentication so the user will not have to sign in more than once. This can be achieved by linking multiple identity profiles associated with the same user to create a federated identity, which would serve as a reliable authentication satisfying both security requirements and user convenience.
Hybrid cloud service providers would also take on a duty to protect all user data, both in terms of corporate responsibility as well as law. User data can be protected through encryption of sensitive data and implementing detailed chronological logs of all user activity relevant to the specific network, such as transactions, communications, authentications, and modifications. These kinds of network tracking strategies are known as audit trails.
Another important security solution is for providers to develop tools to gain full visibility of their cloud networks. Monitoring tools in combination with managed access and data protection can identify abnormal activity, identify risk factors, and enable service agents to follow through on addressing any identified security breaches immediately. Combined with a well trained, responsive staff, these security measures can guarantee a level of security that makes hybrid cloud computing an effective network solution.
Flexible and scalable networks are the future of cloud computing. Growth enables more and more processing power to be handled by the cloud. It is efficient and therefore inevitable that massive networks will interface together to serve multiple purposes creating value for end users. Managed hybrid cloud computing security solutions will play a vital role in achieving the feasibility of such networks.
Featured Image: depositphotos/nils.ackermann.gmail.com